Gartner predicts that by 2025, billions of things will be represented by digital twins .[1] And, by 2021, half of large industrial companies will use digital twins, which could result in an increase in their effectiveness of up to 10%.[2]
But digital twins are still an emerging technology and rely on vast amounts of data. How can you be sure that your digital twin build and deployment is secure?
If you’re working with a vendor, they should have security requirements covered. But do your due diligence and check so you can be sure you are protecting your data, the simulation, and the real-world object or process it represents.
The two sides of digital twin security
The security of digital twins needs to be considered from two sides – the security of the digital twin and the system in which it is implemented, and the security of the real-world object, system, or process it represents.
Although digital twins can help secure IoT devices and processes, the twins themselves can be exposed to risk. Digital twins are software representations that are usually deployed on standard PCs using cloud services for data collection and processing. Software, PCs, and cloud computing have known risks. However, those risks can be mitigated with the proper measures.
What are the risks?
With digital twins being such close and synchronised representations of the real world, unintended access could give hackers an opportunity not only to access the digital twin, but also to conduct penetration testing before hacking the physical system it represents.
If hackers gain access, loss of intellectual property and data, loss of control, and potentially huge costs resulting from down-time, faulty outputs, or data being held to ransom are the most significant risks.
Therefore, to minimise digital twin security risks, it is essential to have a security strategy baked in and implemented from the ground up. A systematic cybersecurity strategy will help eliminate gaps that can otherwise occur between the physical and digital security mirroring and ensuring ongoing hardening of the software.

4 security fundamentals you need to have covered
If you are building and deploying a digital twin, you need it to be fully dependable as decisions based on faulty digital twin outputs can dramatically cost your organisation. Here are the four fundamentals you and your digital twin provider need to consider:
1. Data security and cybersecurity
The digital twin build and deployment needs to be both secure and trustworthy.
Your provider should be securing the data, access to the digital twin, and the real object it’s connected to using robust governance[LS2] practices, authentication, and encryption. Look for two-factor or even multi-factor authentication (2FA or MFA) of the person – not just their device – or use hardware keys. Plus, you need to encrypt data in transit. However, increasingly, it is wise to encrypt data at rest and in use too.
2. Resilience and Dependability
‘Dependability’ encompasses availability, reliability, safety, confidentiality, integrity, and maintainability. These are the attributes that digital twins need to be able to deliver consistently so the outputs can be trusted for business decision making.
However, Laprie suggests the higher need is resilience.[3] He defines resilience as ‘the persistence of service delivery that can justifiably be trusted, when facing changes.’ This is fundamental to digital twins, which need to deliver a high level of service for with correct and trustworthy outputs.
The key threats to dependability are faults, failures, and errors. [4]
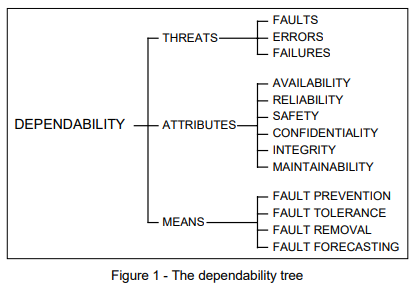
So, you need to make sure your digital twin provider implements and maintain the means for dependability – fault prevention, tolerance, removal, and forecasting – so you can be sure of consistent, reliable outputs you can trust.
3. Privacy
Information privacy is core to any data collection and processing.
Data is personally identifiable, such as location or medical information, its use needs to adhere to all relevant privacy laws such as Europe’s GDPR and California’s CCPA. But even where the data is not personally identifiable, data may need to be kept private to protect intellectual property. Masking, redaction, differential privacy, encryption, and lifecycle management are just a few of the methods that should be available to you in your digital twin deployment to keep data private.
4. Safety
Finally, you need to ensure the safety of the digital twin. Safety may sound basic, but it is a key part of protecting your digital twin and the real system it simulates.
There need [LS3] to be physical locks on doors to the data centre and computer and server rooms, and IT equipment should not be at risk of being damaged either by people, other equipment, or through means like overheating. Never underestimate the fundamentals.

2 security certifications to look for
On top of all the above, your digital twin provider should hold an information security certificate to underscore the trustworthiness of their information handling and the digital twin.
ISO 27001 is an international standard of information security management. Accredited bodies will audit organisations to ensure they comply, and then provide official accreditation or certification. This accreditation requires the organisation to be establishing, implementing, maintaining, and continually improving an information security management system.[5]
A further accreditation that is worth looking for is SOC 2. This is widely recognised as a gold standard for security as the accreditation is based on the organisation achieving a high level of security, availability, processing integrity, confidentiality, and privacy. Organisations with the SOC 2 certification have taken extra measures to protect your digital twin and its data.
As with all security measures, nothing is impenetrable. But ensuring your digital twin provider is certified and enforces proper authentication methods for access will increase your ability to trust the provider and the output of the digital twin simulation for business decision making.
Your action points
Now you know the risks of not having a secure digital twin deployment, here’s the checklist you or your provider need to implement:
- Implement data[SM4] security and cybersecurity
- Use 2FA, MFA, or hardware keys for authentication security
- Use encryption for data in transit, and even at rest and in use
- Increase resilience and dependability with fault prevention, tolerance, removal, and forecasting
- Keep sensitive data private
- Adhere to privacy regulations
- Use masking, redaction, differential privacy, and/or encryption
- Ensure physical safety of the computing assets
- Acquire a globally recognised security certification
Build in security and governance from the ground up when building and deploying digital twins so you have confidence and trust in the end results and outputs. With a digital twin, you can take your product, process, or system to the next level of optimisation and increase your efficiency and profit. So it’s worth getting the security right at the start so none of your hard work is jeopardised.
Do you want to build and deploy a secure digital twin?
Speak to an expert at Slingshot Simulations, the world’s first Simulation-as-a-Service provider. Security is at the core of all our simulations and we can partner with you to build and deploy the digital twins that will take your organisation to the next level.
Contact us here: www.slingshotsimulations.com/get-in-touch
[1] Gartner. ‘Gartner Identifies the Top 10 Strategic Technology Trends for 2019’. (2018) Accessed at https://www.gartner.com/en/newsroom/press-releases/2018-10-15-gartner-identifies-the-top-10-strategic-technology-trends-for-2019
[2] Christy Petty. ‘Prepare for the Impact of Digital Twins’. (2017) Accessed at https://www.gartner.com/smarterwithgartner/prepare-for-the-impact-of-digital-twins/
[3] Jean-Claude Laprie. ‘From Dependability to Resilience’. (LAAS-CNRS, Université de Toulouse, 2008) Accessed at http://2008.dsn.org/fastabs/dsn08fastabs_laprie.pdf
[4] Algirdas Avižienis, Jean-Claude Laprie, Brian Randell. ‘Fundamental Concepts of Dependability’. (UCLA CSD Report no. 010028 LAAS Report no. 01-145 Newcastle University Report no. CS-TR-739, 2001) Accessed at https://www.ppgia.pucpr.br/~alcides/Teaching/SistemasDistribuidos/TOF/avizienis01fundamental.pdf
[5] https://www.iso.org/standard/54534.html
